The bugs that take down production systems, expose customer data, or silently corrupt financial records almost never live in the clever parts of your codebase. They live in the date formatter someone wrote in 2009. The input sanitizer that handles 99.7% of cases correctly. The integer conversion utility that every other module depends on but nobody has opened in four years.
This is not an accident. It is a structural feature of how software teams allocate attention, and until you understand why it happens, you will keep getting surprised by it.
Boring code gets boring treatment
When a senior engineer writes a new distributed consensus algorithm, it gets reviewed carefully. People ask hard questions. They think about edge cases. They write tests that probe the boundaries. The code feels important, so it gets treated as important.
A utility function that parses timestamps from a vendor’s API? Someone wrote it in an afternoon, it worked, and it has been silently running ever since. The tests cover the happy path. The code review, if there was one, took about ninety seconds.
The problem is that “boring” and “low-risk” are not the same thing. That timestamp parser might be called by forty different services. It might be the only thing standing between your system and a heap buffer overflow when the vendor changes their date format. But because parsing timestamps feels like a solved problem, it never gets the scrutiny it deserves.
The most critical code is the code nobody wants to own
There is a category of infrastructure code in almost every mature codebase that does something genuinely important, has no clear owner, and hasn’t been significantly touched since the person who wrote it left the company. I am talking about authentication middleware, connection pool managers, retry logic wrappers, logging formatters.
This code sits at the load-bearing wall of your system. Everything depends on it. But it is not interesting enough to attract talented engineers who want to build new things, and it is not broken enough to justify a rewrite. So it drifts. Edge cases accumulate. The original assumptions, sensible in 2017, quietly stop being true.
The Heartbleed vulnerability in OpenSSL is a clean example of this pattern. The affected code (a bounds check in the heartbeat extension implementation) was not arcane cryptography. It was a routine memory operation of the kind written a thousand times a day. It was boring. That boringness contributed to nobody catching a missing bounds check that exposed private keys for two years across a significant portion of internet infrastructure.
Nobody writes tests for the code that never breaks
Test coverage is not distributed uniformly. It clusters around new features, known problem areas, and anything that has broken in the recent past. The boring utility code, because it has never failed visibly, often has thin or ancient test coverage.
This creates a vicious cycle. Code without tests is harder to refactor safely, so it doesn’t get refactored. As the surrounding system evolves, the untested code gradually drifts out of alignment with the assumptions it was written to satisfy. Nobody notices until a new input shape, a new caller, or a new scale of load reveals the gap.
Your CI pipeline passing does not mean your software is correct. It means your software is correct for the inputs your tests describe. Boring code, with boring tests, is correct for a boring subset of what production will eventually throw at it.
The cognitive bias that makes this worse
Software engineers are not immune to the heuristic that difficulty correlates with importance. When we estimate risk, we tend to anchor on complexity. A brand-new microservice with novel concurrency patterns feels risky. A string parsing function that has been in production for six years feels safe.
This maps onto something cognitive scientists call the fluency heuristic: things that feel easy to think about feel less threatening. Familiar, simple-looking code reads fluently. We scan it quickly and move on, pattern-matching to “this is fine” before we have actually verified that it is fine.
The integer overflow in a counter variable. The off-by-one in an index bound. The unchecked null return from a function that usually returns a value. These do not look scary. They look boring. That is why they survive code review.
The counterargument
The obvious pushback here is that complex code causes more bugs per line. Empirically, this is true. Cyclomatic complexity (a measure of the number of independent paths through code) correlates with defect rates. Novel algorithms have more ways to be wrong.
This is fair, but it misses the point. The argument is not that boring code has more bugs per line. It is that boring code has more severe consequences per bug, and receives less scrutiny per line, which means the expected damage from an undiscovered bug is higher than our instincts suggest.
Complex code that looks complex gets reviewed like complex code. Boring code that carries critical responsibility but looks simple gets reviewed like boring code. The mismatch between apparent risk and actual risk is where the real danger lives.
What to actually do about it
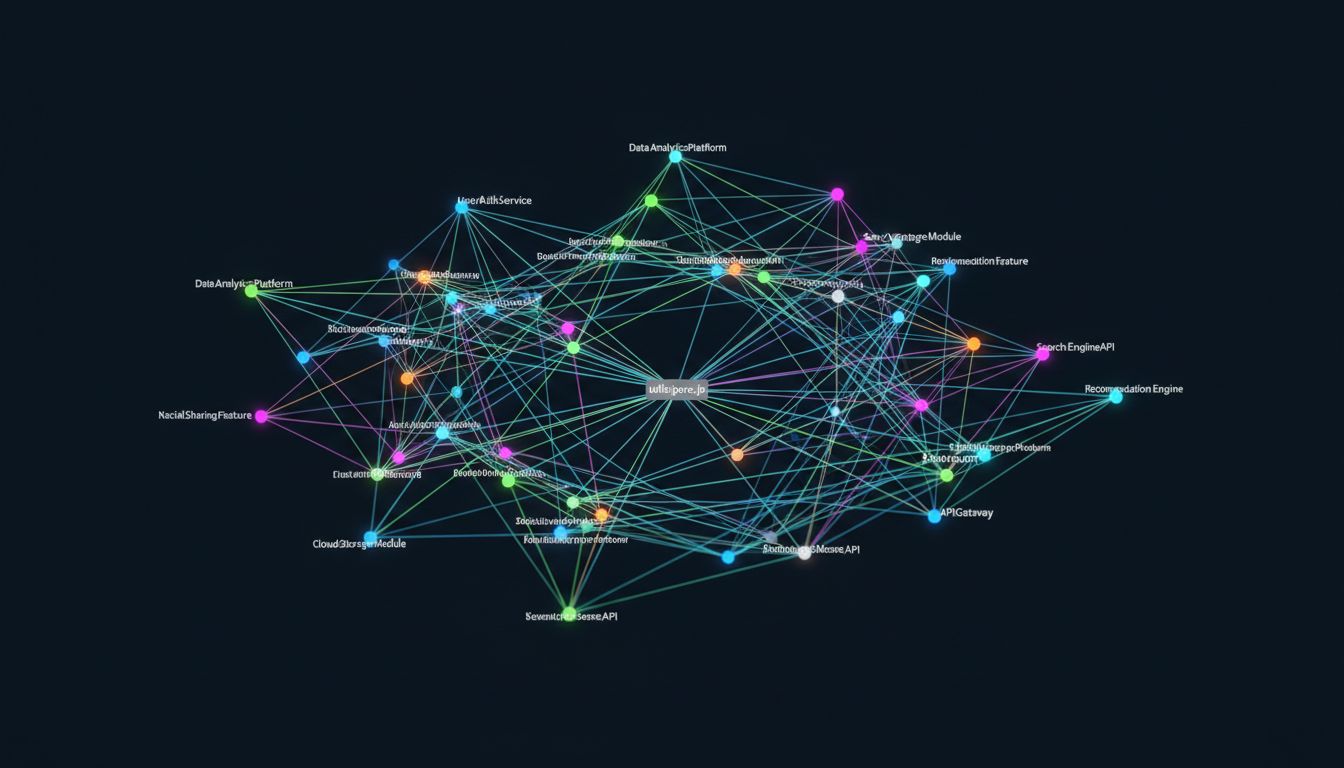
The fix is not to treat all code as equally risky, because it isn’t. The fix is to audit your codebase for what I would call the blast radius of each component, not its apparent complexity. How many callers does this function have? What happens if it returns a wrong value silently? When was it last reviewed by someone who understood the current system context?
Code that scores high on blast radius and low on recent scrutiny is your actual risk surface. It probably looks like the least interesting part of your repository. That is precisely the point.
The dangerous bugs are not hiding in your clever code. They are hiding in the utilities folder, in the shared library nobody wants to maintain, in the six-line helper function that every module imports without a second thought. Go look there first.
