The Simple Version
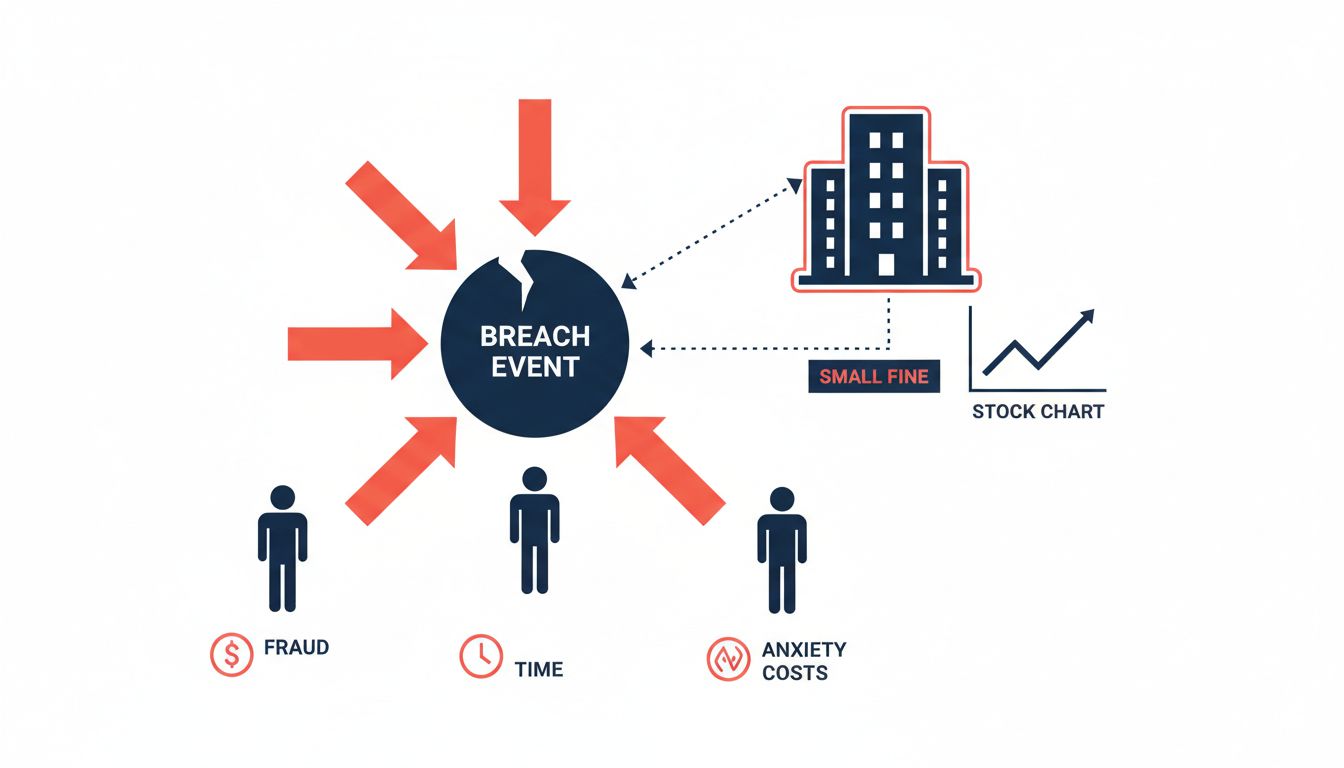
When a company loses your data, the people who suffer are you. The company pays a fine that amounts to a rounding error on its revenue, and life goes on. This isn’t bad luck or regulatory failure. It’s the predictable result of how accountability is structured.
The Costs Land on the Wrong People
Consider what actually happens when your personal data is exposed. You spend hours monitoring accounts, possibly freeze your credit, worry about identity theft for years, and deal with the psychological tax of knowing strangers have your information. The company sends you an email with the subject line “Important Notice Regarding Your Account Security,” offers 12 months of credit monitoring from a third-party service, and moves on.
The asymmetry here is stark. The people bearing the cost (customers) are not the people who made the security decisions (executives and boards). The people who made those decisions answer to shareholders, not to you. And shareholders, it turns out, are remarkably forgiving.
After the Equifax breach in 2017, which exposed the sensitive personal data of roughly 147 million Americans, the company’s stock dropped significantly in the weeks following disclosure. Within two years, it had recovered and then some. Equifax eventually settled with the FTC for up to $700 million, a headline number that sounds large until you realize the company’s annual revenue is around $5 billion. It was an expensive quarter, not an existential threat.
Fines Are Priced In, Not Punitive
Regulatory fines for data breaches are typically calculated based on past harm, not future deterrence. There’s no mechanism that says “this fine should be large enough that no rational company would ever risk this again.” Instead, fines tend to reflect what regulators can politically defend and legally justify, which is almost always less than what would actually change behavior.
The EU’s GDPR was supposed to change this calculus with its famous 4% of global annual revenue ceiling. In practice, enforcement has been slow and inconsistent. Meta was fined 1.2 billion euros by Ireland’s Data Protection Commission in 2023, the largest GDPR fine ever issued. Meta’s annual revenue that year was roughly $135 billion. The math does not suggest a company lying awake at night.
In the US, there’s no federal data breach law at all. The FTC can pursue companies under its unfair practices authority, states have their own patchwork of requirements, and sector-specific rules apply in healthcare and finance. The result is that compliance becomes a legal and lobbying problem, not a security problem.
Switching Costs Protect Incumbents
The obvious market response to a company mishandling your data would be to stop using that company. This works well in competitive markets with low switching costs. It works poorly when the breached company is one of a few options, or when switching means losing years of history, integrations, and workflow.
Equifax, Experian, and TransUnion form an effective oligopoly over consumer credit data. You cannot opt out of their systems in any meaningful way. When Equifax was breached, customers couldn’t leave because there was nowhere to go, and because Equifax’s actual customers (lenders and employers who pay for credit checks) had no particular reason to leave either. Their data wasn’t the data that got stolen.
This pattern appears repeatedly. People stayed on Yahoo after its breaches, which eventually turned out to affect all 3 billion accounts. People stayed on LinkedIn after its 2012 breach exposed over 100 million passwords. People stayed on Adobe, on Marriott, on Anthem. Partly this is inertia. Partly it’s because the alternative often isn’t meaningfully safer, just less used.
The relationship between data collection and business model matters here too. Companies that have built their revenue around data accumulation have a structural incentive to collect more than they secure, because collection drives revenue and security is a cost center.
Disclosure Rules Create the Illusion of Accountability
Most breach notification laws require companies to tell affected customers “in a reasonable time,” which in practice can mean months after discovery. By the time you get the email, the company has already briefed its lawyers, prepared its PR response, and figured out exactly what it’s legally required to tell you (which is usually less than what actually happened).
The notifications themselves are masterpieces of careful language. They tell you what type of data was “potentially accessed” without telling you whether it was actually downloaded, sold, or used. They recommend you “remain vigilant” without defining what that means. They offer credit monitoring, which detects fraud after it happens rather than preventing it.
This theater of accountability gives companies a clear procedure to follow that signals seriousness without requiring any structural change. Execute the notification. Set up the call center. Announce the security review. Move on.
What Would Actually Change Things
The companies that take security seriously tend to do so because their business model depends on it, not because regulators force them to. Payment processors care about security because a breach directly threatens their ability to operate. Banks care because they bear some of the fraud costs themselves. Security is expensive to ignore when you’re the one paying for the downstream consequences.
Extending that logic to other industries would mean shifting more of the breach cost back onto companies. Some legal scholars argue for a strict liability model, where companies owe customers actual damages per record exposed, calculated at a rate high enough to hurt. Others point to the insurance market as a forcing function: as cyber insurance becomes more expensive and selective, underwriters are effectively setting security standards that regulators haven’t.
Neither of these is coming quickly. Lobbying against stricter data liability is well-funded and effective. The companies most exposed to liability reform are also the companies with the most resources to prevent it.
The uncomfortable truth is that data breaches are, for most large companies, a manageable business risk rather than a threat to survival. Until that changes, the incentive to invest seriously in security will stay weaker than the incentive to invest in the response playbook you’ll need when the breach inevitably happens.
