When a major financial services firm discovered that 60% of its data breaches in a recent year originated from home networks, the security team’s first instinct was to blame remote work. They were wrong about the cause, and that misdiagnosis is exactly why the problem keeps getting worse. Remote work doesn’t introduce new vulnerabilities so much as it dismantles the illusion of security that offices provided in the first place.
This distinction matters enormously. Companies that treat remote work as the root cause spend money on the wrong solutions. Those that understand it as a diagnostic tool, one that reveals pre-existing structural weaknesses, build defenses that actually hold. The same pattern shows up in enterprise software design, where surface-level fixes mask deeper architectural problems that eventually surface under stress.
The Office Was Never Secure. It Just Felt That Way.
Corporate offices created what security professionals call a “perimeter model”: a hard shell around a soft interior. Get past the firewall and the badge reader, the thinking went, and you were trusted by default. Employees inside the building shared the same network, the same printers, the same unencrypted internal systems. The model worked reasonably well when most threats were external.
But that assumption had been eroding for years before remote work accelerated it. IBM’s 2023 Cost of a Data Breach report found that the average breach took 204 days to identify, meaning attackers were already inside perimeters, quietly moving through internal systems long before anyone noticed. The perimeter model wasn’t protecting companies. It was giving them false confidence.
Remote work forced organizations to acknowledge what was already true: the perimeter doesn’t exist anymore. Employees access company systems from coffee shops, airports, and home networks shared with smart TVs, gaming consoles, and whatever low-security devices their children use. Each of those devices is a potential entry point. Each home router, often running years-old firmware with known vulnerabilities, is a soft target.
The Real Problem Is Software Sprawl
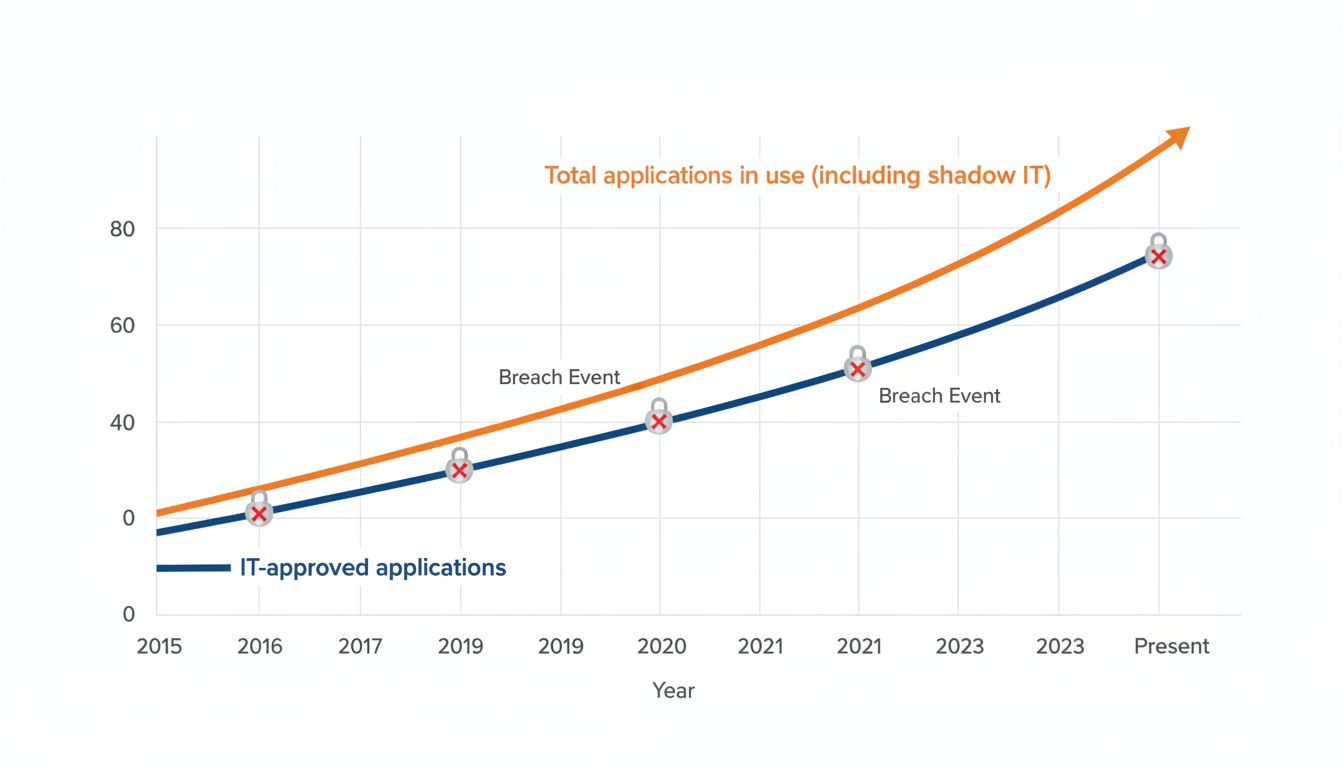
Here is the statistic that should alarm every IT department: the average enterprise employee uses 8 to 10 different software-as-a-service applications in their daily work, according to Okta’s annual Businesses at Work report. In a remote environment, that number climbs. Employees download collaboration tools, file-sharing apps, and productivity software to compensate for the friction of working from home, often without IT approval.
This phenomenon has a name: shadow IT. And it creates a data sprawl problem that is genuinely difficult to solve. When an employee stores a sensitive document in a personal Dropbox, or runs a client call through a free video app their IT team has never audited, they’ve created a data exposure point that the company’s security team doesn’t know exists and therefore cannot monitor.
The subscription software economy makes this worse, not better. Software subscriptions are deliberately structured to encourage proliferation, with low per-seat pricing that makes individual tool adoption feel costless. The actual cost arrives later, measured not in dollars but in attack surface.
Verizon’s Data Breach Investigations Report consistently finds that credentials, meaning stolen usernames and passwords, are involved in roughly 50% of breaches. Every additional application an employee uses is another set of credentials that can be phished, reused from a previous breach, or stored insecurely.
Human Behavior Doesn’t Scale Like Software
Technology often gets blamed for security failures that are fundamentally behavioral. A firewall doesn’t click a phishing link. A VPN doesn’t reuse passwords. People do.
Remote work changes the psychological context of work in ways that matter for security. In an office, there are ambient social cues that reinforce professional norms. The presence of colleagues creates a low-grade accountability that shapes behavior. Working from home removes those cues. Employees make decisions in a more relaxed, informal environment, and that cognitive shift affects how carefully they evaluate suspicious emails.
Research from Stanford psychologist Jeffrey Hancock and others has found that people are measurably worse at detecting deception when they’re fatigued or cognitively overloaded. Remote workers, who frequently manage more interruptions and context-switching than their office-based counterparts, tend to operate in exactly that degraded cognitive state for much of their day. Phishing attacks, which depend on brief lapses in judgment, are optimized for precisely this environment.
This connects to a broader point about how attention and interface design interact. The cognitive science of how habits form around technology interfaces suggests that security training that relies on deliberate recall, rather than ingrained habit, degrades under stress. Security protocols designed for focused office workers may fail when those same workers are distracted at home.
Why Throwing Money at the Problem Doesn’t Fix It
Global cybersecurity spending exceeded $188 billion in 2023, according to Gartner. The number of breaches has not meaningfully declined. This is not a funding problem.
The mismatch stems from how companies diagnose the threat. Organizations tend to invest in tools, more endpoint detection, more VPN capacity, more multi-factor authentication prompts. These are worthwhile investments. But they don’t address the structural issue: remote work exposed that most companies had built security cultures optimized for physical presence, not for a distributed workforce that makes hundreds of small security decisions per day without supervision.
Effective remote security requires three things that budget alone cannot buy. First, a zero-trust architecture that treats every access request as potentially hostile regardless of where it originates, eliminating the dangerous inside-outside distinction of the perimeter model. Second, genuine behavioral change at scale, which requires training that is continuous and contextual rather than the annual checkbox exercise most companies still rely on. Third, a ruthless reduction in software complexity. Fewer tools, properly secured, are safer than many tools loosely managed.
That last point runs against the instincts of many organizations, which respond to security concerns by adding monitoring software on top of an already bloated stack. The evidence consistently points the other way. Simplicity is not a compromise in security architecture. It is the strategy.
The companies that have navigated this well tend to share a common approach: they treated the remote work transition not as an IT problem to be patched, but as an architectural forcing function that required them to rebuild security assumptions from the ground up. That is harder, slower, and more expensive in the short term. It is also the only approach that works.