Hiring the person who just broke into your systems feels, on the surface, like paying a ransom. You are handing a reward to someone who cost you money, embarrassed your security team, and possibly exposed customer data. The logic seems perverse. It isn’t.
The practice of recruiting former attackers, sometimes called “poaching from the dark side” in security circles, is one of the more rational talent strategies in technology. Companies that do it well aren’t being naive or reckless. They are solving a specific, expensive problem with the only resource that actually addresses it: demonstrated capability.
Credentials Don’t Measure What You Actually Need
The security certification industry is enormous. CompTIA, ISACA, and (ISC)² collectively certify hundreds of thousands of professionals each year. What those certifications measure, largely, is knowledge of frameworks, compliance checklists, and documented attack patterns. What they don’t measure is the ability to find a vulnerability nobody has written a framework about yet.
A hacker who successfully breached a major company’s network has demonstrated something no exam can verify: they found a real flaw, in a real production environment, under conditions where the defender was actively trying to stop them. That is a fundamentally different credential. When Microsoft or Google hires through their bug bounty programs, they are essentially running a continuous skills assessment that no structured interview process can replicate.
The skills gap in cybersecurity is not primarily a pipeline problem. It’s a measurement problem. Companies struggle to distinguish between professionals who understand security and professionals who can actually practice it under adversarial conditions.
The Attacker Knows What the Defender Missed
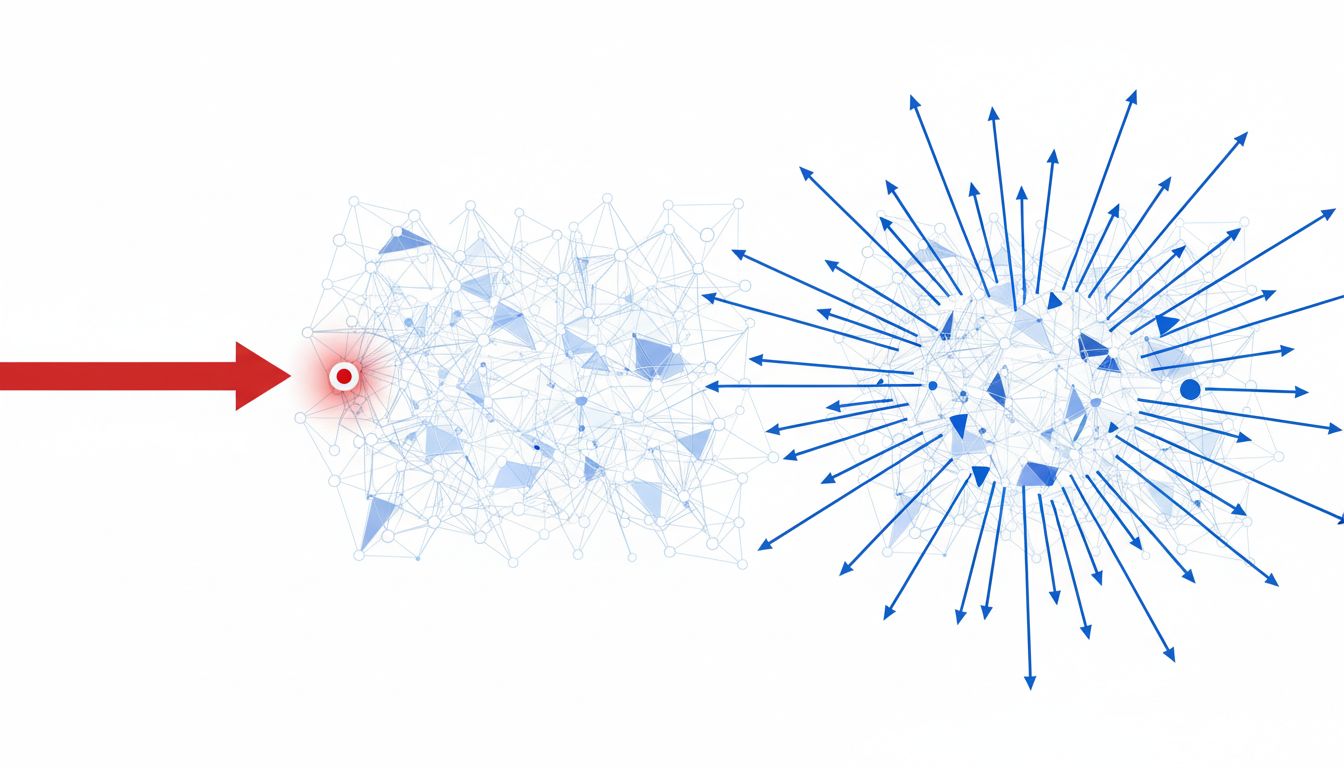
Security teams operate with a structural disadvantage. They have to defend every possible entry point. An attacker only has to find one. This asymmetry means that even excellent defensive teams develop blind spots, often in systems they consider low-priority or in the gaps between tools that each team assumes the other is monitoring.
Someone who successfully exploited one of those blind spots has, by definition, identified a failure mode that the internal team didn’t see. Bringing that person inside converts an adversarial knowledge advantage into an organizational one. Kevin Mitnick, once on the FBI’s most wanted list for computer crimes, spent decades after his conviction as a security consultant to Fortune 500 companies and government agencies. His value wasn’t that he knew networking theory. It was that he had an intuitive, practiced sense of how defensive systems actually fail in the real world, not how documentation says they fail.
This is why companies with mature security programs don’t just hire former attackers: they specifically seek out people who found vulnerabilities that internal teams had missed. The breach itself is the audition.
Bug Bounties Formalized the Relationship
Before bug bounty programs, the relationship between companies and independent hackers was legally ambiguous and adversarial by default. A researcher who found a vulnerability had to decide between disclosing it responsibly (with no guarantee of reward and some risk of legal action) and selling it to parties who would use it maliciously.
Bug bounty platforms, particularly HackerOne and Bugcrowd, changed the structure of that relationship without changing the underlying skill dynamic. Google’s Vulnerability Reward Program has paid out well over $50 million since its launch in 2010. Microsoft, Apple, and Meta run similar programs. These aren’t charity. They are structured talent pipelines that identify the people who found something real and create a documented, legal record of that person’s capabilities.
For many companies, the next step after a significant bug bounty payout is a job offer. The researcher has already proven they can find problems the internal team missed. The bounty payment is essentially a signing bonus paid before the offer is extended.
The Counterargument
The obvious objection is that this practice rewards criminal behavior. If a hacker attacked your systems without authorization, hiring them signals to others that unauthorized access is a viable career path. This concern is legitimate, and it carries more weight when the person being hired crossed clear legal and ethical lines, particularly in cases involving data theft, extortion, or attacks on critical infrastructure.
There is a meaningful distinction between a researcher who found and disclosed a vulnerability (even aggressively or imperfectly) and someone who monetized an attack against your customers. Companies that blur this distinction do create a bad incentive structure. Hiring a ransomware operator because they are technically skilled is not the same as hiring a bug bounty researcher who found a critical flaw and wanted to negotiate the terms of disclosure.
The more principled version of this practice, which is what most major companies actually do, draws that line clearly. Bug bounty programs exist partly to provide a legal channel for exactly this kind of talent identification. The goal is to hire people who operate in the gray zone of aggressive research, not people who operate in the black market.
What This Practice Actually Reveals
The deeper point here isn’t really about reformed hackers. It’s about what companies reveal when they adopt this strategy. They are acknowledging that the formal credentialing system in security is not reliably identifying the people who can actually do the job. Big tech’s approach to talent acquisition often reflects this same underlying logic: when conventional hiring signals fail, companies build alternative pipelines that measure demonstrated performance instead.
Hiring a former attacker is uncomfortable precisely because it makes explicit what most talent strategies prefer to leave implicit: credentials are a proxy for capability, and a weak one. When you have direct evidence of capability, the proxy becomes unnecessary.
Companies that hire former attackers aren’t being reckless. They are being honest about what they need and where to find it.
