The instinct in security circles is to treat paper as a legacy weakness, a holdover from before encryption and zero-trust architecture. The opposite is true. The organizations most serious about protecting their highest-value information, including intelligence agencies, central banks, and the most security-conscious technology companies, still rely on paper for their most sensitive material. This is not nostalgia. It is sound risk management.
The core thesis is simple: a document that has never touched a network cannot be exfiltrated through one. Every cybersecurity control, however sophisticated, assumes adversaries will probe it. Paper does not make that assumption because it does not need to.
The Attack Surface Problem
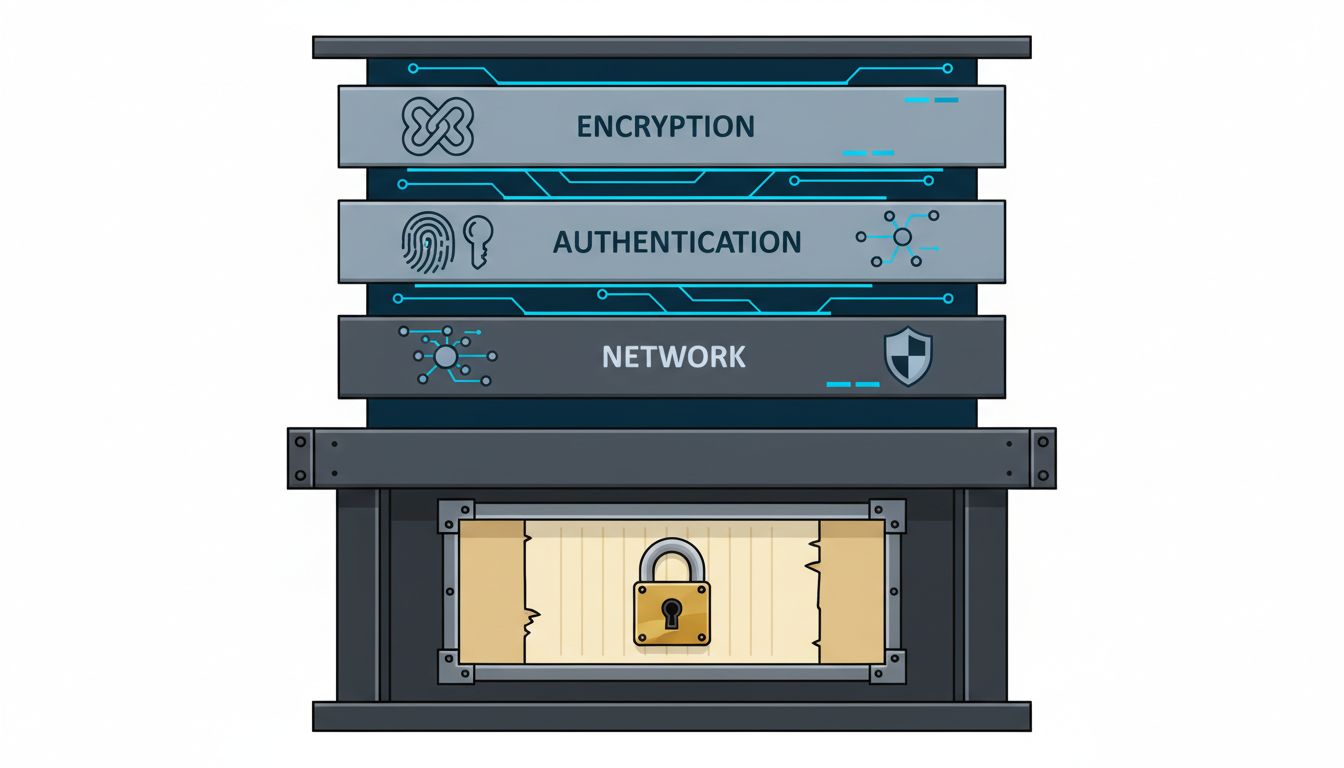
Every digital system has an attack surface. Encrypt a file and you have to store the encryption key somewhere. Put the key in a hardware security module and you have to manage access credentials for the module. Layer in multi-factor authentication and you introduce the telecom infrastructure those factors depend on. Each solution adds security but also adds surface.
Paper removes this chain almost entirely. The U.S. intelligence community still uses paper-based one-time pads for certain communications categories. Nuclear launch authorization procedures involve physical documents partly because the authentication chain for a digital system creates vulnerabilities the physical system avoids. These are not organizations that failed to hear about modern cryptography. They have simply done the threat modeling and concluded that for certain data, offline physical storage beats networked digital storage.
The asymmetry matters. A sophisticated nation-state actor can probe a digital system continuously, automatically, from anywhere in the world. Getting to a paper document requires physical access, which dramatically narrows the field of capable adversaries.
The Insider Threat Dimension
Most high-profile data breaches are not the result of external hackers defeating encryption. They involve insiders, whether malicious or negligent. A Verizon Data Breach Investigations Report from recent years found that insider threats account for a substantial fraction of confirmed breaches, and the proportion is higher in finance and healthcare than in other sectors.
Paper handles this differently, not better in every dimension, but differently in ways that matter. Copying a digital file leaves no physical trace unless logging is configured correctly and reviewed consistently. Copying a paper document requires physical action: a photocopier, a phone camera, or a hand-written transcription. Each of these creates evidence. The physical bulk of paper also creates a natural checkpoint at building exits in ways that a USB drive or an email does not.
This is why law firms handling the most sensitive merger negotiations sometimes print documents and collect phones at the door of certain conference rooms. The security model is not about preventing every possible leak. It is about ensuring that any leak requires deliberate physical effort and leaves a trail.
The Cyber Attack Scenario
Consider what happens when a company’s systems are compromised by ransomware. Everything on the network is either encrypted by the attacker or treated as potentially compromised. The incident response protocol typically involves taking systems offline, which means losing access to the very records needed to manage the response.
Organizations that maintain paper copies of critical operational procedures, emergency contact trees, network diagrams, and recovery playbooks can continue functioning while their digital infrastructure is offline. This is not a hypothetical. Hospitals hit by ransomware attacks have reverted to paper records to maintain patient care while their systems were restored, a scenario that has played out at health systems across the United States and Europe in recent years.
The point is not that paper is better than digital for routine operations. It is not. The point is that paper and digital serve different functions in a mature security posture, and treating paper as merely obsolete misunderstands what it does.
The Counterargument
The strongest objection to paper is physical security. A stolen laptop with strong encryption is nearly useless to an attacker. A stolen paper document is immediately readable. Paper can burn, flood, or simply be lost. You cannot audit who has read a paper document the way you can audit a digital access log. These are real limitations.
The response is not that paper defeats digital security on every dimension. It is that paper defeats it on the specific dimension that matters most for certain categories of information: network-based exfiltration. The threat model determines the right medium. For a company’s routine customer data, paper would be absurd. For a board’s deliberations about an acquisition that would move a stock price substantially, or for a cryptographic seed phrase controlling a large cold-storage wallet, paper held in physical security becomes rational.
The mistake is treating security as a single axis from weak to strong. It is a matrix of threats, and different mediums have different profiles across it.
The Right Tool for the Right Threat
The companies that understand security best do not default to digital because it is modern or default to paper because it is familiar. They ask which threats they are most concerned about and which medium best addresses those threats for a specific class of document.
For the crown jewels, the information whose exposure would be most catastrophic, the answer keeps coming back to paper, physical access controls, and a complete absence from any network. This is not a failure of imagination about digital security. It is the product of taking digital security seriously enough to understand its structural limits.
Security theater involves adding complexity that looks impressive. Real security involves removing attack surface wherever the cost of removal is lower than the cost of defending it. For the most sensitive documents in the most secure organizations, the cost of removing network exposure is printing. That is a trade worth making.