How Bad Advice Got Institutionalized
In 2003, a software engineer at the National Institute of Standards and Technology named Bill Burr published an eight-page document that would quietly shape how hundreds of millions of people log into computers for the next two decades. His advice: use uppercase letters, numbers, and symbols. Change your password every 90 days. Avoid recognizable words.
Burr later told the Wall Street Journal he regretted most of it. The guidance was based on a 1980s white paper about mainframe security, not any empirical study of how real people create and remember credentials. But by the time the regret was published, in 2017, the advice had already been baked into corporate IT policies worldwide, encoded in password-creation forms that rejected anything that looked too simple, and taught to a generation of users as received wisdom.
The result was predictable in retrospect: people responded to complexity requirements by being consistently, systematically predictable. They capitalized the first letter. They put the number at the end. They replaced the letter ‘a’ with ‘@’ and the letter ‘o’ with ‘0’. Attackers figured this out quickly. Password-cracking dictionaries now include thousands of these substitution patterns as a matter of course.
What Attackers Actually Measure
To understand why the conventional advice backfired, you need to understand what a password is actually defending against. There are two primary attack methods: credential stuffing (using username-password combinations leaked from other breaches) and brute-force cracking (systematically guessing passwords against a stolen hash database).
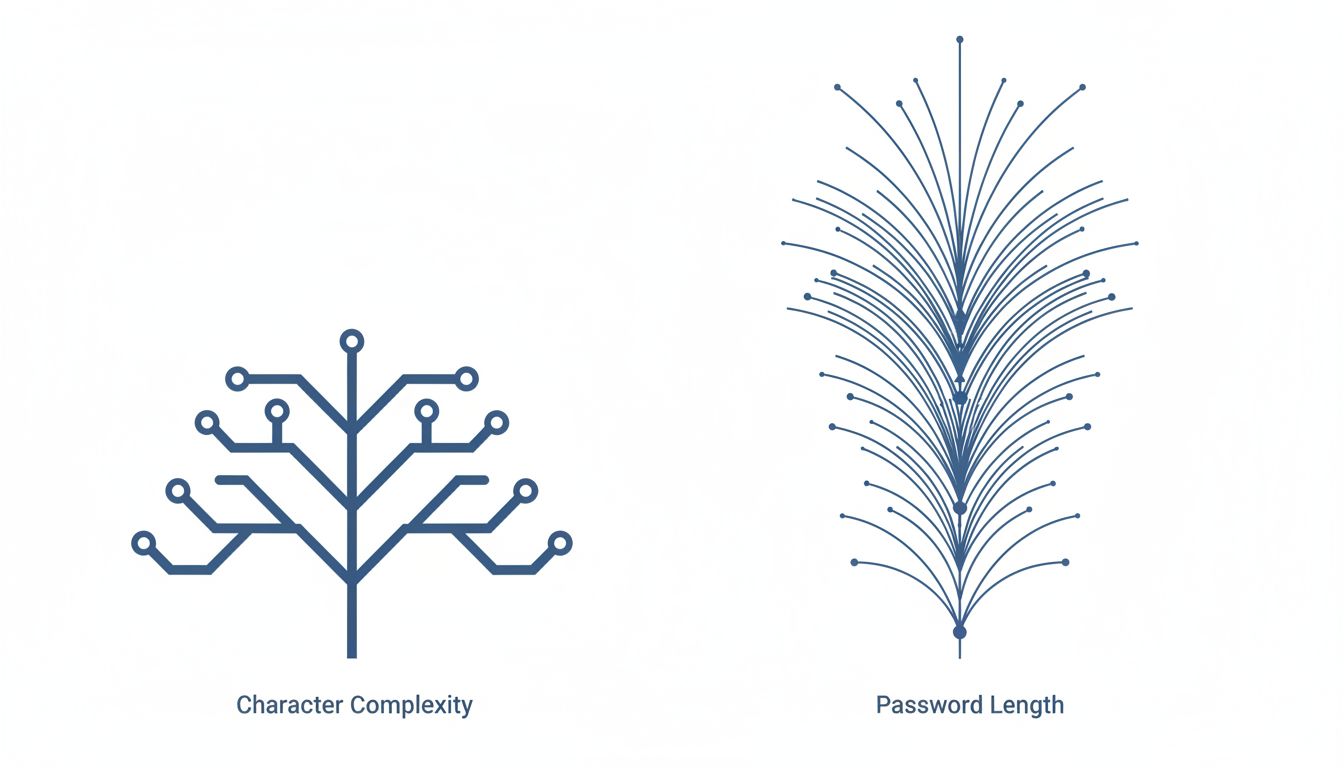
For brute-force attacks, what matters is entropy: the number of possible combinations an attacker must try. Entropy is a function of two variables, the size of the character set and the length of the password. Crucially, these don’t contribute equally. Length compounds. Adding one character to a password multiplies the search space by the size of your character set. Adding a special character increases the character set from roughly 62 options to roughly 94, a factor of about 1.5. Adding one more character at that character set size multiplies the search space by 94.
This means a longer password built from simple words is frequently stronger than a shorter password with mandatory complexity. The phrase “correct horse battery staple” (popularized by the webcomic xkcd in 2011) has approximately 44 bits of entropy if words are chosen randomly from a common dictionary. A typical eight-character complex password sits around 40 to 50 bits depending on how it was constructed. The passphrase wins or ties, and it takes about three seconds to memorize.
The Memorability Trap Nobody Talks About
Here is where the security community missed something important: a password that gets written on a sticky note or reused across 12 accounts has effectively zero entropy, regardless of how complex it looks.
Verizon’s annual Data Breach Investigations Report has consistently found, across multiple years, that stolen or weak credentials are involved in the majority of confirmed data breaches. Not zero-day exploits. Not nation-state hacking. Passwords that were reused, leaked, guessed, or written down. The attack surface that complexity requirements were supposed to shrink turned out to be dominated by human behavior, not cryptographic weakness.
This creates a practical principle that security researchers have been converging on: usability and security are not in tension for passwords. They are, at a certain level of abstraction, the same thing. A password system that causes users to reuse credentials or store them insecurely produces worse security outcomes than a system that allows simpler credentials that users actually manage properly.
NIST revised its guidance in 2017, largely abandoning the complexity requirements Burr had codified. The updated SP 800-63B guidelines recommend prioritizing length over complexity, eliminating mandatory rotation for passwords that haven’t been compromised, and checking new passwords against lists of known-breached credentials rather than enforcing character-class requirements. Major enterprise adoption of this guidance has been uneven, partly because IT departments spent years building policy infrastructure around the old rules.
Why Passphrases Work (and When They Don’t)
The passphrase approach has real merit under specific conditions. Four or more randomly chosen words from a large dictionary can generate enough entropy to resist offline cracking, provided the words are actually chosen randomly and not constructed from meaningful personal phrases.
This is the critical caveat. “MyDogNamedRocky2015” is a passphrase in the technical sense but not in the security sense. It’s a meaningful sentence that follows predictable human patterns: proper noun, pet, year. Attackers running dictionary attacks against cracked hashes already account for this. Real passphrase security requires random selection, which is why methods like Diceware (literally rolling dice to select words from a numbered list) exist. The randomness isn’t a procedural nicety. It’s load-bearing.
For sites where you won’t need to type the password manually and where a breach database is less likely to be targeted, a passphrase remains a strong and practical choice. For high-value accounts like email, banking, and anything tied to financial or identity information, a passphrase combined with multi-factor authentication produces significantly better outcomes than complexity requirements alone ever could.
The Password Manager Question
The obvious objection to all of this is that password managers solve the underlying problem. If a piece of software generates and stores unique, high-entropy credentials for every account, the memorability question becomes irrelevant for most logins. You only need to remember one master password, which you can make genuinely strong because it’s the only one.
This is correct, and password managers are worth using. But they don’t make the memorability question go away entirely. You need to remember the master password, obviously, and ideally know it well enough to type it under pressure without a hint. More importantly, password managers have their own failure modes. LastPass suffered a significant breach in 2022 in which attackers obtained encrypted password vaults, meaning anyone with a weak master password was at immediate risk. The security of the entire system collapsed to the strength of the one credential users actually had to remember.
There’s also the access problem. Password managers require setup, trust, and consistent use across devices. Adoption outside of technically literate users remains limited. For the majority of people who are not using a password manager, and there are many of them, the question of what makes a good memorable password is not theoretical.
What the Research Says About Memory and Security
Cognitive research on memory offers a useful frame here. Humans are significantly better at remembering episodic and narrative content than arbitrary strings. We remember stories, sequences of events, and concrete images. We are poor at remembering strings of characters that have no semantic relationship to each other.
This is exactly why “Tr0ub4dor&3” is both hard to remember and, as a category, less secure than it looks. It’s arbitrary enough that we can’t use narrative memory, but rule-governed enough that attackers can systematically guess it. Passphrases composed of concrete, imageable words exploit the brain’s actual strengths. “correct horse battery staple” produces a mental image, however absurd, that sticks.
Some security researchers have explored this further, looking at whether associating a password with a distinctive visual scene or mini-narrative improves both recall and resistance to common attacks. The results suggest that the same properties that make a passphrase memorable, concreteness and mild unexpectedness, also reduce the risk of predictable patterns.
This connects to a broader theme in how security policy gets designed. Systems are frequently optimized for the behavior of a hypothetical rational actor, then deployed to real humans who behave differently. The gap between the model and the reality becomes an attack surface. Password complexity requirements are a clear case study in that failure mode.
What This Means
If you’re managing password policy for an organization, the core adjustment is straightforward: prioritize length minimums over character-class requirements, check new passwords against breach databases (services like Have I Been Pwned make this accessible via API), and stop mandating rotation on a fixed schedule. Rotate on confirmed compromise, not calendar date.
If you’re an individual user not yet using a password manager, a four-word random passphrase from a large dictionary provides strong protection for most accounts and is practical to memorize. The word “random” matters: personal phrases, pet names, and meaningful dates do not provide equivalent security regardless of length.
If you are using a password manager, the one password worth spending real effort on is your master credential. Make it long, make it genuinely random, and verify you can recall it without the manager available.
The underlying principle is that security models which fight human memory rather than work with it tend to lose. Not because users are careless, but because memory is a real constraint, and systems that ignore real constraints produce predictable failures.