In 2019, a mid-sized logistics company in the American Midwest signed a seven-figure contract with a supply chain software vendor. The agreement looked standard. The integration timeline looked reasonable. The limitation of liability clause, buried in section 14.3 of a 40-page master service agreement, capped the vendor’s total financial exposure at twelve months of subscription fees.
Twelve months of fees was roughly $280,000.
When the implementation failed eighteen months later, corrupting inventory records across three distribution centers and triggering a cascading fulfillment breakdown during peak season, the actual damages ran well past $4 million. The company’s legal team quickly understood what had happened. They had effectively self-insured for the gap between $280,000 and $4 million without knowing it.
The Clause Is Everywhere
This is not a story about an unusually predatory vendor. The limitation of liability clause, often styled as a “mutual” cap, is standard language in virtually every enterprise software agreement sold today. Salesforce uses it. Oracle uses it. SAP uses it. So does nearly every SaaS vendor pitching to mid-market buyers who lack dedicated procurement counsel.
The structure is almost always the same: liability is capped at fees paid in the prior twelve months (sometimes six), consequential damages are excluded entirely, and the carve-outs for gross negligence or willful misconduct are written so narrowly that they rarely apply in practice.
The clause is mutual in name. In practice, it is deeply asymmetric. The vendor’s risk is bounded by a contractual ceiling. The buyer’s risk is bounded only by how badly things can go wrong.
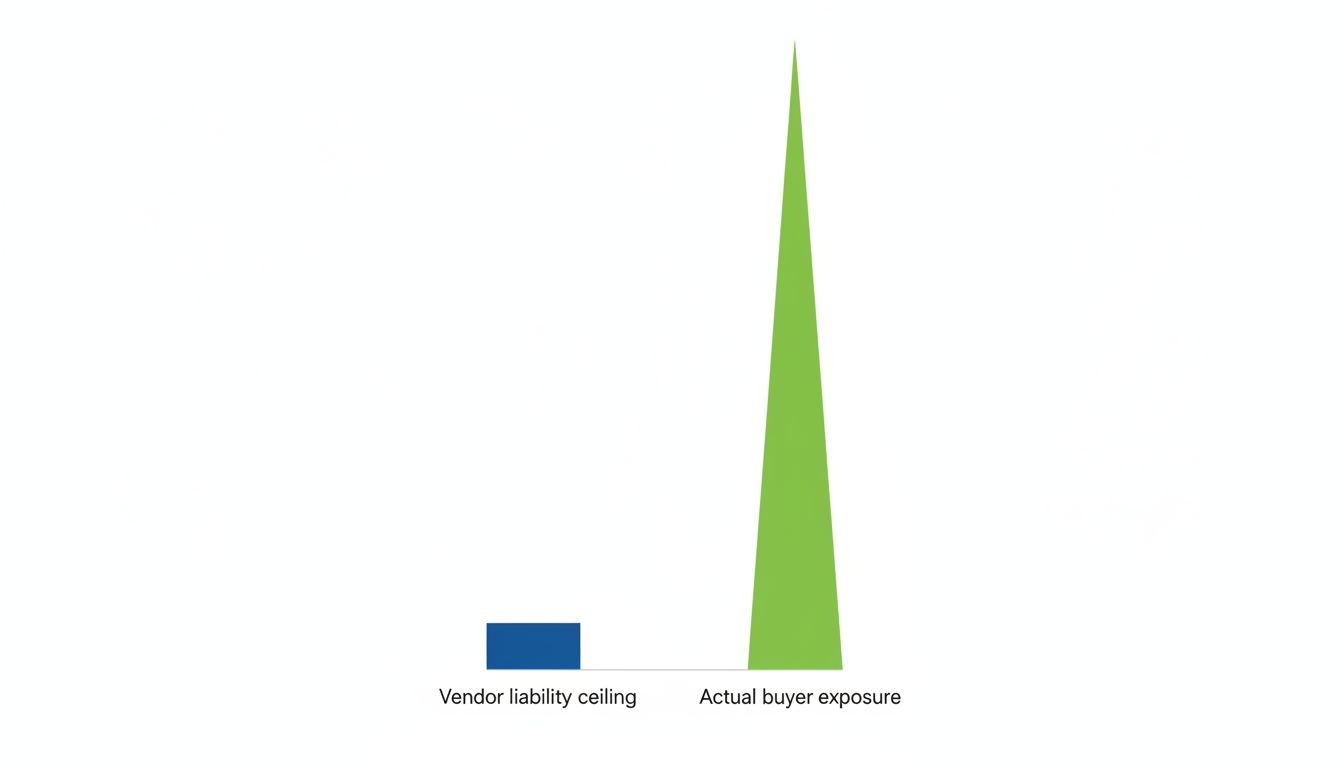
The math clarifies the problem fast. A company paying $500,000 annually for ERP software is exposed to whatever downstream damage a failure creates: production halts, customer penalties, regulatory fines, emergency remediation costs, reputational damage. A poorly executed migration at a manufacturer can idle a factory floor. A data breach at a healthcare system can trigger HIPAA investigations. The software vendor’s maximum exposure: $500,000. The buyer’s maximum exposure: genuinely unlimited.
This is not a theoretical risk. The 2020 SolarWinds breach produced damages that cascaded through thousands of organizations, many of which discovered their software contracts provided essentially no path to recovery from the vendor. Knight Capital’s 2012 trading algorithm failure, while internally caused, illustrated how quickly software errors produce financial damage that dwarfs any conceivable contractual recovery. The clause isn’t a footnote. It is the actual risk allocation mechanism for some of the most consequential technology relationships companies enter.
Why Buyers Sign Anyway
The logistics company’s procurement team wasn’t negligent. They were outgunned. The vendor’s contract team had negotiated hundreds of these agreements. The buyer’s team was reviewing a contract for a software category they were implementing for the first time, under deadline pressure from a board that had already approved the budget.
This is the normal condition. Enterprise software vendors are specialists in their own contract terms. Buyers are generalists encountering those terms once every several years. The information asymmetry is structural, and vendors benefit from it.
There is also a psychological dimension. By the time a contract reaches signature, both sides have invested months in sales cycles, proof-of-concept work, and relationship building. Renegotiating section 14.3 feels like accusing the vendor of planning to fail. Procurement teams frequently wave through boilerplate because challenging it feels adversarial and the project champion has already told the CFO the deal is done.
Vendors know this. The clause is positioned late in the agreement, after the commercial terms that buyers actually read. It is written in the same dense legal prose as every other section, with no visual distinction to flag its economic significance.
What Negotiated Terms Actually Look Like
The clause is not immovable. Large enterprise buyers with leverage negotiate modifications routinely, which is precisely why the practice is common in vendor contracts with smaller buyers: it only sticks where it goes unchallenged.
A competent negotiation for a high-stakes implementation typically pursues several modifications. First, expanding the liability cap to a multiple of annual contract value (two to five times is achievable for critical systems) rather than a single year. Second, carving out specific damage categories, particularly data loss, security breaches, and implementation failures that corrupt production data, from the consequential damages exclusion. Third, requiring the vendor to maintain errors-and-omissions insurance at meaningful coverage levels and naming the buyer as an additional insured.
None of these modifications are exotic. They are standard asks from experienced procurement teams at companies large enough to have them. The problem is that a significant portion of enterprise software buyers lack that experience.
The Deeper Issue
The limitation of liability clause is a symptom of something more fundamental: software vendors have successfully exited the traditional risk-sharing model that governs most commercial relationships.
When a construction contractor builds a defective structure, liability follows the damage. When a pharmaceutical company ships a flawed product, the tort system provides a recovery mechanism. Software vendors have, through decades of contract standardization and judicial deference to limitation-of-liability clauses, created a category where catastrophic failure is possible, probable in a meaningful percentage of complex implementations, and largely the buyer’s financial problem.
This matters more as software becomes more deeply embedded in operational infrastructure. A SaaS payroll system that misfires doesn’t just cause inconvenience. It creates regulatory exposure, employee relations crises, and potential labor law liability for the buyer. The vendor’s contract limits recovery to a year of subscription fees. The downstream consequences are uncapped.
The 99.9% uptime SLA that vendors advertise as a reliability commitment is, from a contractual standpoint, often meaningless without a liability framework that makes breach of that SLA financially consequential. An SLA with a liability cap is essentially a promise the vendor has structurally pre-limited the cost of breaking.
What to Actually Do
The logistics company eventually settled with the vendor for an amount that covered roughly half their documented losses, largely because their counsel identified specific misrepresentations in the implementation scoping process that created separate liability exposure. That’s not a replicable strategy. It’s a lucky break in a bad situation.
The actionable lesson is earlier and less dramatic: before signing any contract for software that touches revenue-generating operations, the limitation of liability section needs the same scrutiny as the pricing terms. The relevant questions are direct. What is our realistic downside if this implementation fails or this vendor has a serious security incident? Is the liability cap a meaningful fraction of that downside? If the answer to the second question is no, the contract as written transfers substantial unpriced risk to the buyer.
For companies that genuinely lack the procurement infrastructure to negotiate these terms, a narrower version of this analysis is still useful: at minimum, understand what risk you are holding. The company that signs a capped contract knowing they are self-insuring for the gap is in a materially better position than the company that signs it assuming the vendor is responsible for the consequences of their own failures.
The clause will not disappear. Vendors have no rational incentive to volunteer more exposure. But buyers who understand what they are agreeing to can at least price the risk correctly, push for modifications where they have leverage, and stop being surprised by section 14.3 when something goes wrong.
