The encryption protecting most sensitive data today is, for practical purposes, unbreakable. AES-256, properly implemented, would take longer than the age of the universe to brute-force with current computing. Attackers are not sitting in basements running decrypt loops. They stopped trying to break encryption years ago, because they found something far easier: everything around it.
1. Encryption at Rest Means Nothing If the Keys Live Next Door
A database encrypted with AES-256 is genuinely secure as a mathematical object. The problem is that the application reading that database needs the decryption key at runtime, and that key has to live somewhere. In practice, it often lives in a configuration file, an environment variable, or a secrets manager that the compromised application can query freely.
The 2019 Capital One breach is the clearest modern example. The attacker did not crack encryption. They exploited a misconfigured web application firewall to obtain credentials, then used those credentials to request data from AWS services directly. The data was technically protected by encryption. The key access controls were not. Over 100 million customer records were exposed.
2. TLS Protects the Tunnel. Not the Endpoints.
When you see the padlock icon in your browser, it means the data in transit is encrypted using TLS. That is a real protection and worth having. What it does not mean is that the server on the other end is trustworthy, that the data is encrypted once it arrives, or that the application handling it is secure.
Most breaches targeting web applications happen after the TLS handshake completes. SQL injection, cross-site scripting, and server-side request forgery attacks all operate on plaintext data inside the application layer, after the encrypted tunnel has done its job. The encryption was working perfectly. It just was not the relevant defense.
3. Phishing Gets Keys Without Touching the Algorithm
The simplest bypass is also the most common: ask someone with legitimate access for their credentials. Phishing attacks do not require any cryptographic knowledge. They require a convincing email and a user who enters their password on the wrong page.
The 2022 Uber breach was executed by an 18-year-old who used social engineering to obtain an employee’s VPN credentials, then spammed multi-factor authentication push notifications until the employee accepted one. Every layer of encryption Uber deployed remained intact and irrelevant. Once authenticated, the attacker had the same access to internal tools and data as any legitimate employee.
4. Key Management Is Where Most Organizations Actually Fail
Cryptography has a well-understood answer for most threats: use strong keys, rotate them regularly, store them separately from the data they protect, and limit which systems can access them. This is called key management, and the gap between knowing this and actually doing it in a complex production environment is enormous.
Many organizations use the same encryption key for years because rotating it requires coordinating across systems, updating application configs, and handling the transition window where old and new keys are both valid. That coordination cost is real, and teams under pressure skip it. A static key that never rotates becomes a single point of failure for every record encrypted under it.
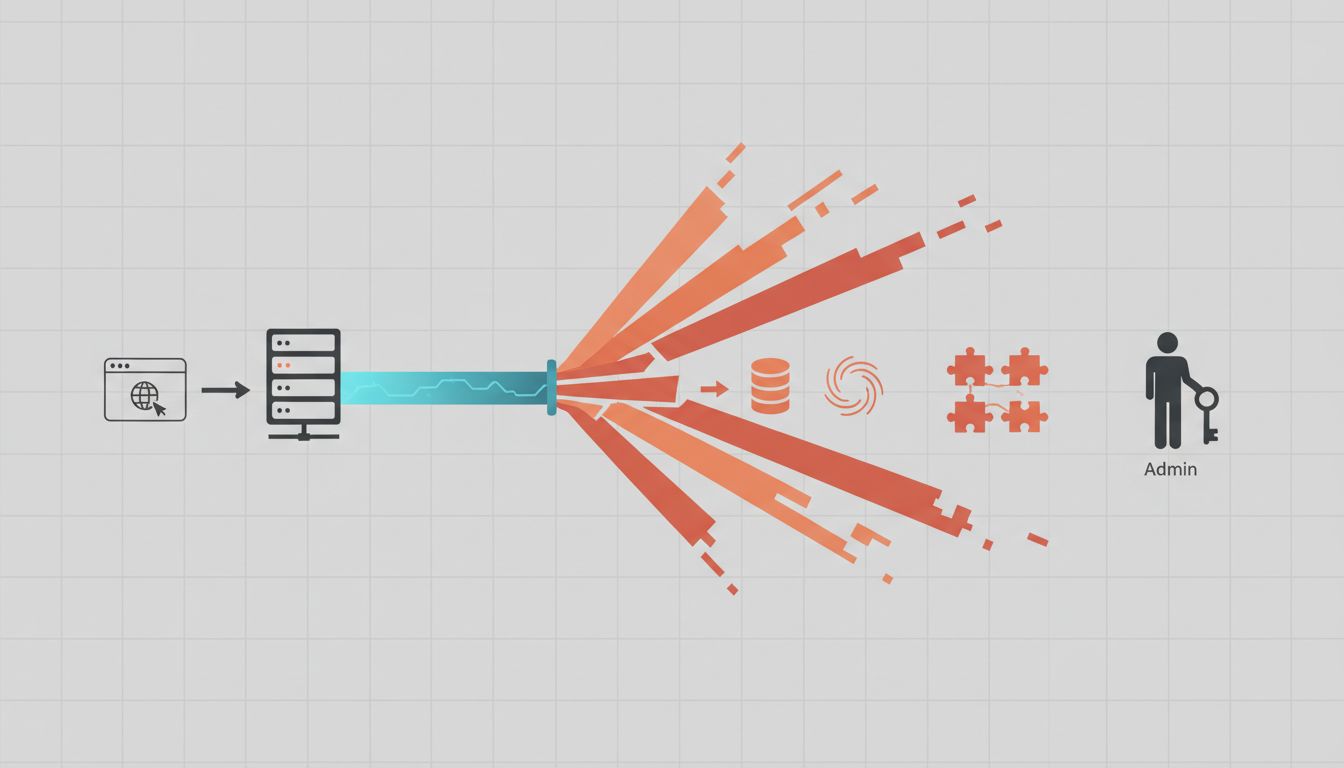
5. Third-Party Access Is a Perimeter You Rarely Audit
Most enterprise systems grant access to vendors, contractors, and SaaS integrations that the security team did not fully vet and the engineering team does not actively monitor. Each of those integrations is a potential path to data that encryption alone cannot protect.
The 2013 Target breach is still the textbook case. Attackers gained entry through credentials stolen from a third-party HVAC vendor that had network access for billing and contract purposes. That access was never supposed to reach payment systems, but network segmentation was insufficient. Millions of credit card records were stolen. Target’s encryption of stored card data was compliant with industry standards. The lateral movement path through a vendor with excessive access was not something encryption could address.
6. Logging and Monitoring Gaps Let Breaches Run for Months
Encryption protects data confidentiality. It does nothing for detection. An attacker with valid credentials can exfiltrate encrypted data by decrypting it through the application layer, and if there are no alerts on unusual query volumes or access patterns, that exfiltration can continue for a long time.
The Marriott breach disclosed in 2018 had begun in 2014, when Starwood’s systems were first compromised. The attacker had four years of access before detection. The data was not unprotected because encryption was absent. It was unprotected because nobody noticed the ongoing access. Detection and response capabilities are a separate discipline from encryption, and organizations that invest heavily in one while neglecting the other are not as protected as their compliance checkboxes suggest.
7. Memory and Processing Are Unencrypted by Design
For encryption to be useful, data must eventually be decrypted and processed. At the moment of processing, in RAM, data exists in plaintext. Attacks targeting this window include RAM scraping malware (which is exactly how most large retail payment breaches have worked) and cold boot attacks, where an attacker with physical access extracts memory contents before they clear.
This is not a flaw in AES. It is a fundamental property of how computation works. Fully homomorphic encryption, which would allow computation on encrypted data without decrypting it first, exists as a research area but carries performance costs that make it impractical for most production systems today. Until that changes, every system that processes sensitive data has a window where the data is exposed, and securing that window is an operational and architectural problem, not a cryptographic one.
The takeaway is not that encryption is overrated. It is that encryption is one layer in a defense-in-depth strategy, and organizations that treat it as a finish line rather than a starting point are systematically exposed. The math is solved. The surrounding architecture usually is not.