The Misconception Built Into the Word ‘Encrypted’
Most people picture encryption as a single operation: a message goes in, scrambled text comes out, the other person unscrambles it. That picture is wrong, and the gap between the mental model and reality matters more than it seems. The actual process that runs when you tap send on Signal or iMessage involves at least four distinct cryptographic operations, a handshake protocol, and a key management system sophisticated enough to protect messages you haven’t written yet. Understanding this is not just technically interesting. It explains why some systems that call themselves encrypted are meaningfully less secure than others.
The confusion runs deep partly because the word “encryption” gets used as a catch-all. Transport Layer Security (TLS), which protects your bank login, is encryption. A ZIP file with a password is encryption. End-to-end encryption in Signal is also called encryption. They use overlapping math but make completely different security guarantees, and collapsing them into one word does real damage to how people reason about their own privacy.
The Key Exchange Problem and How Modern Protocols Solve It
Before any message content can be protected, two parties who may never have met need to agree on a shared secret over a channel that could be monitored by anyone. This sounds impossible. The solution, called a Diffie-Hellman key exchange, is one of the stranger ideas in applied mathematics: two parties can each contribute to a shared value that neither of them ever transmits in full. An eavesdropper who sees every packet exchanged during setup still cannot reconstruct the shared secret without solving a problem (the discrete logarithm problem) that is computationally infeasible at the key sizes used in practice.
Signal’s protocol, which also underlies WhatsApp’s encryption layer, extends this further with something called the Extended Triple Diffie-Hellman (X3DH) key agreement. Before you ever send your first message to someone, Signal’s servers have already stored a set of precomputed public keys for that person, including a batch of one-time-use keys called one-time prekeys. When you initiate a conversation, your client uses a combination of these keys to derive a shared secret without the other person even being online. This is why Signal can establish a new conversation immediately even when your contact has not opened the app in a week.
What the Double Ratchet Is Actually Doing
Once a session is established, Signal and similar apps use what is called the Double Ratchet Algorithm to manage encryption for individual messages. The name describes the mechanism accurately: two ratchets, advancing in tandem, each responsible for a different kind of forward protection.
The first ratchet, a Diffie-Hellman ratchet, turns whenever new key material is exchanged between devices (which happens regularly and automatically). The second, a symmetric-key ratchet, advances with every single message. The result is that each message is encrypted with a key that is derived from, but cryptographically distinct from, every previous key in the chain.
The practical consequence is a property called forward secrecy. If an attacker somehow compromises the key used for message 47, they still cannot decrypt messages 1 through 46, because those keys have already been derived and discarded. They also cannot trivially decrypt message 48, because the ratchet will have advanced. This is a materially stronger guarantee than systems that encrypt all traffic under a single long-lived key. In those systems, one successful compromise retroactively exposes everything.
This also explains a behavior that sometimes confuses users: encrypted messaging apps do not let you read old messages on a newly installed device the way Gmail lets you read old email. The keys that decrypted those messages are gone. There is no server-side copy to retrieve them from. That is a feature, not a limitation.
Where the Chain Actually Breaks
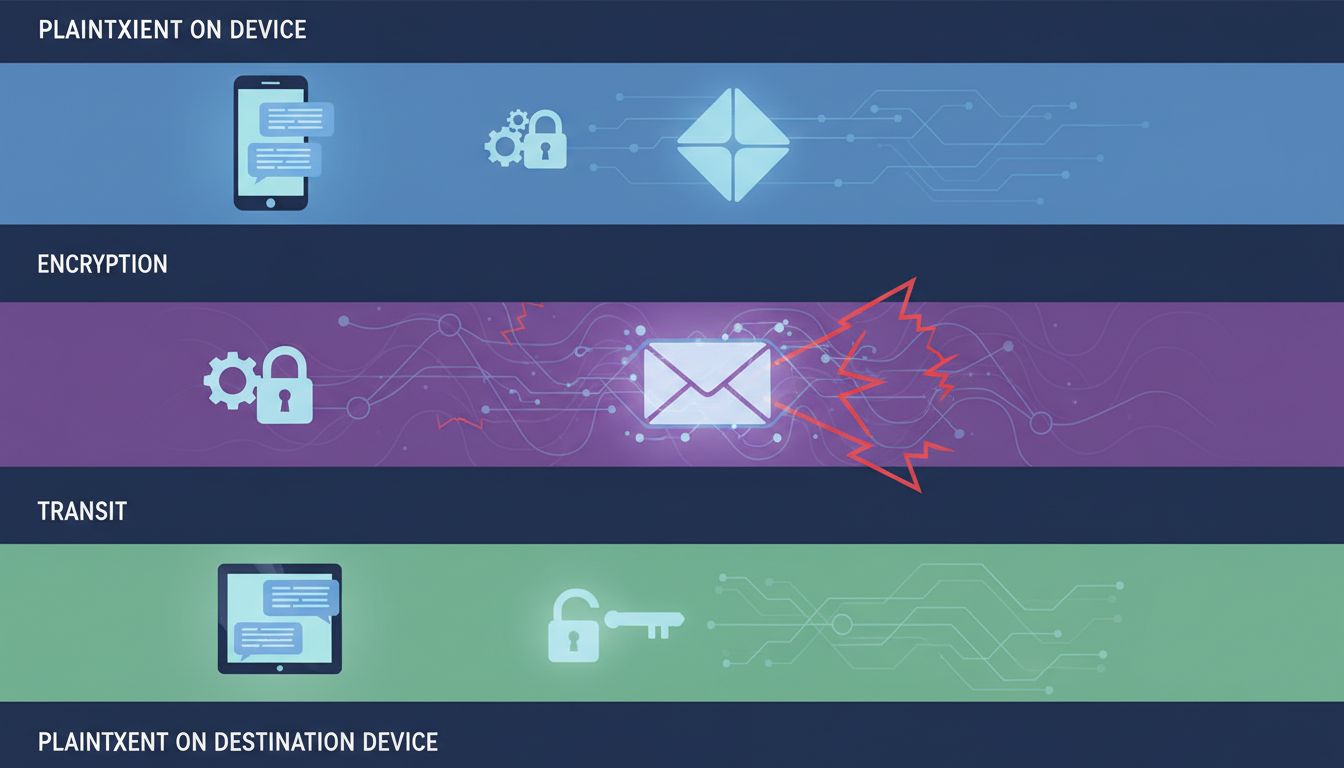
All of this cryptographic machinery protects the message in transit and creates strong guarantees about what an attacker who intercepts packets can learn (essentially nothing useful). What it does not protect is the message at rest on either device, the metadata surrounding the communication, or the trustworthiness of the endpoints themselves.
Metadata is worth taking seriously as a distinct threat. Signal encrypts message content completely. What it cannot fully hide is that you sent a message to a particular person at a particular time, because routing a message requires the network to know its destination. In 2013, NSA documents published by The Guardian described a program that collected this kind of metadata at scale, explicitly on the theory that content was less valuable than the map of who was talking to whom and when. Encrypting content addresses one problem. It does not address that one.
Endpoint compromise is the more common practical vulnerability. If someone has installed spyware on your phone, they can read your messages before they are encrypted, because they are sitting at the point in the chain where the plaintext exists. Law enforcement agencies in multiple countries have pursued this approach when encryption itself proved resistant. In 2021, reporting on the Pegasus spyware project by Forbidden Stories and Amnesty International documented how targeted devices could be compromised without any user interaction, giving attackers access to messages in apps with strong encryption. The cryptography worked exactly as designed. The device did not.
The Architecture Reflects Specific Threat Models
The reason this matters beyond technical curiosity is that choosing a messaging tool is implicitly choosing which threat model you trust the developers to have solved. Signal’s architecture, with its ephemeral keys and no message backups to the cloud by default, is optimized against server compromise and retroactive decryption. iMessage with iCloud Backup enabled is considerably more accessible to legal process, because the keys needed to decrypt your messages are stored by Apple. Google’s RCS implementation varies in what it protects depending on carrier and configuration.
None of this makes one tool unconditionally better than another for every person. A journalist communicating with a source has different threat priorities than someone who is mainly worried about data breaches at a messaging company. The architecture of the cryptographic system is what determines which threats it addresses and which it leaves open.
The 200 milliseconds it takes to send an encrypted message contain a key agreement, a ratchet advancement, authenticated encryption of the message content, and a routing operation that reveals less than a standard SMS but more than nothing. Understanding this chain does not require being a cryptographer. It requires being willing to read the security model rather than just the marketing.
